The AI Vulnerability Storm: Getting "Mythos-Ready" Before It Hits
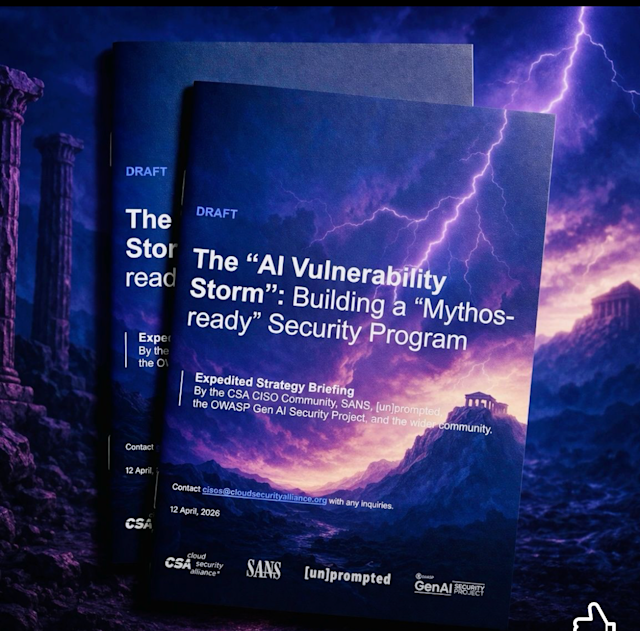
A new briefing from the Cloud Security Alliance, SANS, and a coalition of over 50 industry leaders—including former NSA Cybersecurity Director Rob Joyce—is one of the most important cybersecurity documents of 2026. If you work in tech, you should read it.
The subject is Mythos, Anthropic's latest AI capability, and what it means for every organization's security posture. The short version: the window between vulnerability discovery and weaponization has collapsed from weeks to hours, and it is not coming back.
What Mythos actually does
Mythos autonomously found thousands of critical zero-day vulnerabilities across every major operating system and browser. It generated working exploits without human guidance at a 72% success rate—compared to twice under identical conditions for the prior generation model. It discovered a 27-year-old OpenBSD bug. It did this at machine speed, without elaborate setup or expert configuration.
In response, Anthropic launched Project Glasswing, giving selected vendors early access to patch their products before disclosure. It is a meaningful effort. It cannot cover everything.
Why this is a structural problem
AI gives attackers a disproportionate advantage. It lowers the cost and skill required to find and exploit vulnerabilities faster than organizations can patch them. Defenders are still constrained by the same testing, validation, and deployment cycles. That gap is widening, not closing—and comparable capabilities will spread to open-source models within months.
What "Mythos-ready" means in practice
The CSA briefing lays out a practical framework organized around three priorities:
- Defend at machine speed: Point AI agents at your own code now. Use tools like Claude Code or open-source equivalents to find vulnerabilities in your systems before attackers do. Make AI agent adoption mandatory, not optional.
- Harden the fundamentals: Network segmentation, phishing-resistant MFA, egress filtering, and accurate asset inventory. Every boundary raises attacker cost. You cannot defend what you do not know exists.
- Update your risk models: Pre-AI assumptions about patch timelines and exploit scarcity are outdated. Boards and executives need an honest picture of what has changed—including what it means for reporting and regulatory exposure under the EU AI Act.
The opportunity
The same tools that empower attackers also empower defenders. Organizations that adopt AI agents for security will move faster and find weaknesses first. The briefing's closing comparison is apt: Y2K was a systemic threat met through coordinated, disciplined effort. This is that kind of moment.
The briefing is free, authoritative, and actionable. Read it.
Read the full document: The "AI Vulnerability Storm": Building a "Mythos-ready" Security Program — CSA, SANS, OWASP, and with host of luminary contributors.
Published April 2026 | Cloud Security Alliance CISO Community